Introduction
Within the automotive industry, the concepts of Hardware Security Modules (HSMs), Hardware Security Engines (HSEs), and Secure Hardware Extensions (SHEs) play pivotal roles in ensuring the security and integrity of critical systems and sensitive data. While these technologies share the common objective of enhancing security, their applications and functionalities differ significantly. This technical article aims to explore the distinctions between HSMs, HSEs, and SHEs within the context of the automotive sector, shedding light on their specific implementations and benefits.
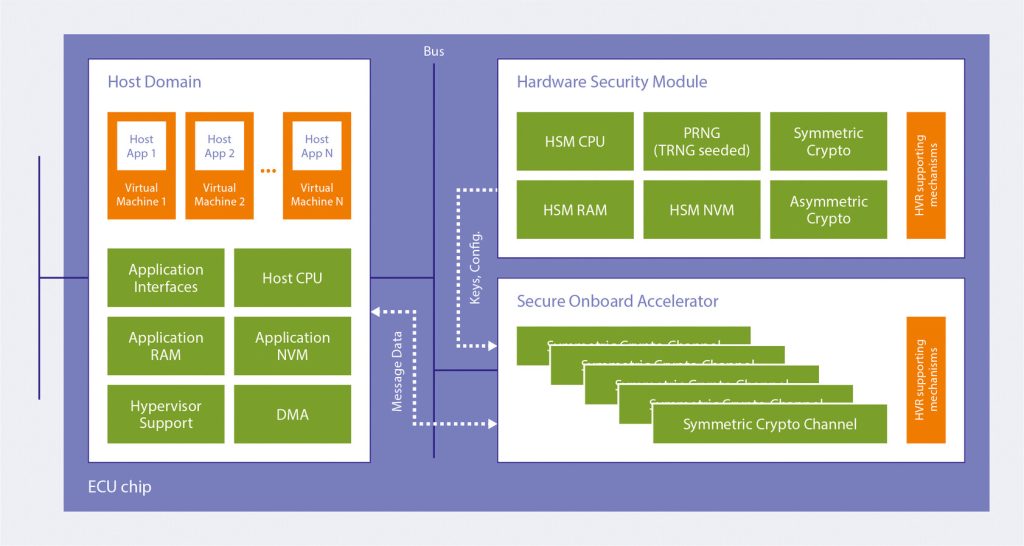
Hardware Security Module (HSM)
n the automotive industry, a Hardware Security Module (HSM) serves as a dedicated cryptographic device designed to bolster security in various aspects of automotive systems. HSMs are deployed to protect sensitive information, facilitate secure communication, and ensure the integrity of critical operations within connected vehicles. They provide robust security mechanisms and key management capabilities to address the unique challenges faced by the automotive industry, such as securing vehicle-to-vehicle communication, protecting firmware updates, and ensuring trusted software execution.
Key Applications of HSMs in Automotive:
- Secure Communication: HSMs enable secure communication channels between Electronic Control Units (ECUs) within the vehicle, ensuring confidentiality, integrity, and authentication of data transmission. This includes secure messaging protocols, secure remote access, and secure vehicle-to-infrastructure communication.
- Firmware Updates: HSMs play a crucial role in securing Over-The-Air (OTA) software updates for automotive systems. They authenticate the firmware updates, verify their integrity, and ensure that only trusted and authorized software is installed on the vehicle, preventing unauthorized modifications and potential vulnerabilities.
- Key Management: HSMs securely store cryptographic keys used for various purposes, such as vehicle access, authentication, encryption, and digital signatures. They protect these keys from unauthorized access and provide secure key provisioning mechanisms.
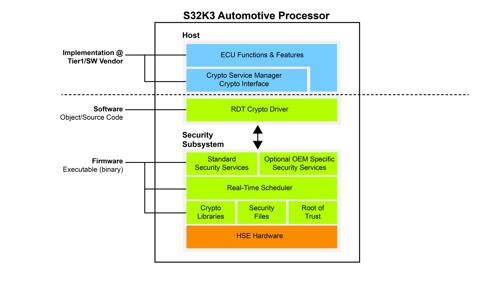
Hardware Security Engine (HSE)
In the automotive industry, a Hardware Security Engine (HSE) refers to a specialized hardware component integrated into automotive systems to accelerate cryptographic operations, providing enhanced security and performance capabilities. HSEs are designed to offload computationally intensive cryptographic tasks from the main processor, ensuring efficient and secure cryptographic operations without compromising system performance.
Key Applications of HSEs in Automotive
Secure Communication Protocols: HSEs accelerate cryptographic operations used in secure communication protocols, such as Transport Layer Security (TLS) and Secure Sockets Layer (SSL). This ensures fast and efficient encryption and decryption of data during secure data transmission between the vehicle and external entities.
Digital Signatures: HSEs provide hardware acceleration for generating and verifying digital signatures. This enables the authentication and integrity verification of data, ensuring that messages or software components originate from trusted sources and have not been tampered with.
Secure Storage: HSEs offer hardware-based secure storage capabilities, allowing automotive systems to securely store encryption keys, certificates, and sensitive data. This protects against unauthorized access, theft, or tampering of critical information.
Support for hardware-accelerated secure boot processes to ensure trusted and tamper-proof software execution.
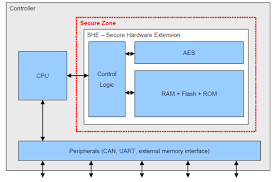
Secure Hardware Extension (SHE)
Secure Hardware Extensions (SHEs) in the automotive industry refer to integrated security features or modules within microcontrollers or System-on-Chip (SoC) devices. SHEs provide hardware-based security features to strengthen the overall security posture of automotive systems. These features include secure boot processes, secure storage for encryption keys, tamper detection mechanisms, and secure debug interfaces. SHEs help ensure the integrity and confidentiality of critical functions within automotive systems and protect against potential attacks.
Key Applications of SHEs in Automotive:
- Secure Boot Processes: SHEs enable secure boot processes to verify the authenticity and integrity of software during the vehicle’s startup. This ensures that only trusted and verified software components are executed, mitigating the risk of running malicious or unauthorized code.
- Secure Storage: SHEs provide secure storage mechanisms for cryptographic keys, sensitive data, and secure firmware updates. This protects against unauthorized access, tampering, or extraction of critical information from the vehicle.
- Tamper Detection and Response: SHEs incorporate tamper detection mechanisms to identify physical attacks or unauthorized attempts to manipulate or access critical system components. These mechanisms trigger appropriate responses, such as disabling certain functions or initiating security protocols, to mitigate potential threats.
- Secure Debug Interfaces: SHEs offer secure debug interfaces that prevent unauthorized access to critical system resources during debugging or maintenance activities. This ensures that only authorized entities can access and interact with sensitive components of the automotive system.
Conclusion
In the automotive industry, Hardware Security Modules (HSMs), Hardware Security Engines (HSEs), and Secure Hardware Extensions (SHEs) serve distinct yet complementary purposes in bolstering the security and integrity of critical systems and sensitive data. HSMs ensure secure key management, cryptographic operations, and protection of sensitive information. HSEs provide hardware-accelerated cryptographic capabilities to enhance system performance while maintaining security. SHEs offer hardware-based security features, such as secure boot processes, secure storage, tamper detection, and secure debug interfaces, to protect against potential attacks and ensure the integrity of automotive systems. Understanding these differences is crucial for automotive manufacturers and developers aiming to implement robust security measures tailored to the unique requirements of the automotive industry.